In today’s world, where work and personal computing are increasingly intertwined, it’s crucial to understand the importance...
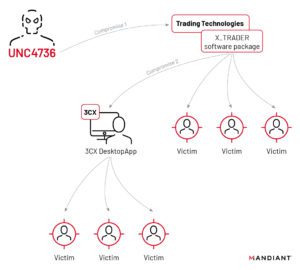
🔓 #3CX hit by a groundbreaking double #SupplyChainAttack! 😲 North Korean hackers target #Crypto businesses via a...
Protect your system from the critical CVE-2023-23397 vulnerability in Microsoft Outlook! Learn how to fix it and...
Improve your software development with CI/CD! Learn how to automate updates and deployments with Kubernetes and popular...
“Collaboration in SaaS can create high-risk situations if links are shared without caution. Learn best practices for...
Microsoft report links Iranian Mint Sandstorm APT to US critical infrastructure attacks, utilizing new tactics and targeting...
UK NCSC and US agencies issue joint advisory on APT28’s exploitation of Cisco routers in 2021, highlighting...
Breaking down barriers between IT and Security teams is key to a successful partnership. Learn how to...
Beware of NoName057(16)’s DDosia project – their cyber warfare activities threaten the safety of websites in Europe....
Digital attackers are getting smarter, using existing tools on PCs to breach systems. The Netherlands is a...